I’m wanting to know what permissions a user is required to have in order to stop and start AlwaysUp services. Is there a way to grant access to specific users as I don’t want to have to give them full Admin rights? I’ve created shortcuts but getting the “access denied” message. Thanks in advance.
I’m wanting to know what permissions a user is required to have in order to stop and start AlwaysUp services. Is there a way to grant access to specific users as I don’t want to have to give them full Admin rights? I’ve created shortcuts but getting the “access denied” message. Thanks in advance.— Bryant, Wide Bay Water
Hi Bryant.
Typically, only administrators have the power to control Windows Services. That is an appropriate stance, as most services are administrative in nature.
Indeed, it would be a huge mistake to allow non-privileged persons to stop any of the important tasks servicing the computer in the background. Think of the chaos it could cause!
But there are always exceptions. And the good news is that Microsoft provides the ability to set granular permissions on each Windows Service. You can leverage that API/functionality from command-line tools like Microsoft’s SubInACL but your best option is to work directly with AlwaysUp (which is much easier to use).
How to adjust the rights of an AlwaysUp Windows Service
Follow these steps to grant a non-admin user the ability to start and/or stop your service:
Start AlwaysUp.
Highlight/select the application you wish to grant access to. Stop it if necessary.
Select Application > Advanced > Service Security Settings from the menu.
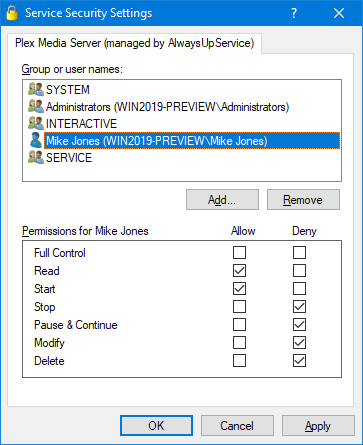
In the Service Security Settings window that comes up, select the user in the top pane. You will have to add the account if it’s not there.
In lower pane, choose the permissions you wish the user to have.
Here you see us permitting user “Mike Jones” to read/access and start (but not stop) the Plex Media Server service:
Save your changes.
Afterwards, the user will be able to use the Services Control Panel application, the NET command or the SC utility to manipulate the service created by AlwaysUp.
Remember: The user must work with the full, quoted name of the service, with the “managed by AlwaysUp” suffix. For example, if your application entry is named “VirtualBox” in AlwaysUp, the service will be named:
“VirtualBox (managed by AlwaysUp)”
Easily adjust the rights of non-AlwaysUp Windows Services too!
The instructions above will work for AlwaysUp services, but our free Service Security Editor tool can adjust the permissions of any service. Check it out if you need a general, portable solution for all your Windows Services.